Here is a fast-access list of the top dark web sites for those ready to explore the hidden networks, broken down by category. Remember that these are onion sites and dark web websites, and their addresses are highly dynamic:
- DuckDuckGo: The privacy-focused search engine’s Tor mirror, great for clearnet searches.
- OnionFind: The dark web search engine that helps users find active .onion websites while maintaining anonymity.
- Amazon Market: Polished dark web marketplace that facilitates the trade of illegal goods using cryptocurrency and escrow systems.
- Tenebris: It is a dark web forum (a community hub) that has grown in popularity for discussions about darknet activities, market law enforcement news, and uncovering scams.
- Ahmia: It is a legitimate and well-regarded search engine that indexes both clearnet and .onion links.
- Torch: One of the oldest and largest independent dark web search engines.
- Haystak: Comprehensive search engine that boasts a huge index of Tor websites.
- OnionWiki: The original community-maintained directory of Dark Web Links. (Caution required as always.)
- ProPublica: The respected investigative journalism website with a secure Tor web address.
- BBC Tor mirror: The official BBC News mirror, providing uncensored access worldwide.
- The New York Times: Official Tor mirror for journalists and readers in censored regions.
- Proton Mail on Tor: An anonymous, encrypted email service that operates an onion site for maximum privacy.
- SecureDrop: A platform for anonymous submission of documents to news organizations by whistleblowers.
- Keybase: A secure digital identity service that allows for encrypted chats and sharing of files.
- Dread: A platform for online discussion about the darknet, like ‘Reddit for the Darknet.’
- SearX: Privacy-focused metasearch engine that delivers unbiased search results without tracking users or logging their queries.
- OnionLinks: A verified, organized directory providing updated and categorized .onion addresses.
- Riseup: A collective providing secure email and chat services for activists.
- CIA’s .onion URL: The Central Intelligence Agency’s official Tor site for anonymous tip submissions.
- Facebook onion site: Official Tor mirror for users in countries with strict censorship.
- Archive.today: A snapshot service that preserves web pages even after they have been taken down.
- Sci-Hub: A massive database providing access to scientific articles and academic books.
- ExoneraTor: A service from the Tor Project to check if an IP was used as a Tor relay at a given time.
- Tor Metrics: Provides public statistics and data on Tor usage, growth, and security.
- Tails: The official site for Linux OS, the recommended operating system for accessing the Dark Web.
- Deep Web Radio: Anonymous dark web streaming platform that broadcasts music 24/7 while allowing users to share and contribute playlists.
Note: Visiting the hidden corner of the internet (dark web) requires you to be extra cautious about your setup. Before you go (if you must), make sure you’re running a trusted VPN like NordVPN to cloak your connection and shield your identity. It’s your first layer of defense in staying private and secure online.
The dark web brings to mind visions of dark deals and shady places to buy and sell things. But this area of the Internet is more than that—it is a necessary layer of the Internet for journalists to communicate with their sources, activists to dodge censorship, and regular people to regain their privacy in terms of communication.
If you want to use the Tor browser to search for websites that are accessible only via the hidden networks, dark web links (.onion addresses), you should be aware of both where to find them and how to remain secure while visiting these locations.
In this article, we share our list of the 28 best dark web sites today, which include verified, trusted, and safe options to use when exploring the Dark Web.
Protect yourself first: Dark web security tips

Accessing the dark web may not be illegal in most areas, but you should be prepared for the chance of encountering illegal/harmful content. If you follow these steps, you will have an excellent chance of being able to explore “safe” dark web content that poses minimal risk to yourself.
Identify Your Intent: Do not go in without a search for anything – go in with a goal (Example: “I am looking up the ProPublica site”). By having a defined goal, you will reduce the chance of accidentally coming across any illegal content.
- Follow the VPN-tor rule: You may consider it safe to browse the dark web using your VPN service along with the Tor browser. Doing so will keep your Tor activity private from your ISPs.
- Disable scripts: In the Tor Browser Security Slider, set it at the “Safest” Option to disable JavaScript and other components commonly used to distribute malware and de-anonymize users.
- Don’t download files: If you are unsure about where a file originated or whether it is trustworthy – like when you visited an official news organization’s SecureDrop page – do not download anything from Tor! Files like PDFs, docs, pics, and executables are how you get malware.
- Do not use personal information: If you intend to enter the dark web, you should never disclose your true identity while on the dark web (your actual name, email address, etc.) or use any of your normal email accounts (such as a Gmail account) for any of the online accounts you visit while using the TOR browser.
- Verify onion URLs: Onion URLs are long, random character combinations. There is rampant typosquatting (keeping the same names/spellings of sites where users enter information incorrectly) on the dark side of the internet. You must copy and paste onion URLs from verified directories and make sure to carefully check the URL bar.
- Stay within the law: Although using the Dark Web is not illegal, if you are trying to keep yourself out of legal trouble, it is crucial that you know that if you participate in illegal activity such as buying drugs or engaging in criminal activity with the intent of hacking into a system, or distributing child pornography or any other type of material used for child exploitation, you will violate many laws in nearly every country around the world. Accessing and using TOR also does not provide full anonymity to users. Law Enforcement is active in monitoring activity in this space.
The essential access toolkit: Safely accessing the dark web
To safely access any dark web links, you must first have two essential tools that provide anonymity while maintaining your digital identity.
1. Tor Browser – Your connection path
The Tor network (“The Onion Router”) gives access to the Dark Web. The Tor network utilizes various randomly selected relay points whereby, through encrypting the internet data originating from the user, there can be no way of determining where the connection originated from.
The onion routing system of Tor means it does not allow for a person’s specific physical address or any location, and therefore, an individual cannot easily determine the way you arrived on the dark web.
2. VPN (The PS Solution) – Your foundation of security

Tor only provides anonymity for your usage on the Tor network; it does not hide the fact that you are using Tor from the ISP, and the ISP will still potentially flag your account or your activity for using the Tor network.
The only way to protect your identity from your ISP when you connect to the Tor network is by utilizing a premium VPN service. (While paid services offer more features, some reputable free VPNs can provide a basic layer of privacy; see our guide to best VPNs for the dark web for options.)
By using a VPN together with Tor, you get the added benefit of encryption from both services, which provides additional security due to overlapping coverage. People commonly refer to this type of service as “Tor-over-VPN.”
The following is a breakdown of how the two services protect your privacy:
- Your Internet Service Provider (ISP) observes the encrypted data as it travels to the VPN server.
- The VPN observes the encrypted data as it travels to a Tor entry node.
- The Tor Network sees the IP Address of the VPN Server and not your actual IP Address.
Using this method protects your anonymity while you browse the top dark net sites by masking your identity with two layers of privacy between you and the websites.
Best dark web sites – The detailed list of more than 25 Tor links

Below, we share 26 dark web links you can explore. But, as noted earlier in the article, before you start, you should install a quality VPN like NordVPN to stay safer online and protect your identity.
1. DuckDuckGo
- Direct onion link: https://duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion/
This is also a recognized name within the clearnet community for its specialization in maintaining user privacy. DuckDuckGo never tracks its users, and it maintains no record of users’ search history. DuckDuckGo’s .onion service offers Tor users the same level of privacy that the service now provides to clearnet users; this is an essential first step because of the privacy aspect of this type of search engine.
While DuckDuckGo does not provide Dark Web search results themselves, DuckDuckGo’s .onion service is a type of safety net and will be the first place to check if you want to confirm you are anonymous after you’ve opened the Tor browser and before you go into the more hidden areas of the dark web. Therefore, DuckDuckGo will provide the first, safest place to search on the Dark Web.
For many, DuckDuckGo’s onion site serves as the ultimate proof that you can utilize the Tor network for completely legitimate, everyday internet needs without sacrificing privacy.
2. OnionFind
- Direct onion link: http://ofinde3b67voi7xiq3qflof2mwriwngicd7glwvf3bclgdgcjfozlzqd.onion/
OnionFind is a reliable dark web search engine designed to help users discover onion sites with ease. Although some search results may be duplicated or no longer active, it remains a practical option for locating working .onion links while keeping your identity protected.
Unlike DuckDuckGo’s Tor version, OnionFind focuses exclusively on .onion results. You can use it through its clearnet website, OnionFind.com, or access it directly within the Tor browser for a more private experience.
3. Awazon Market
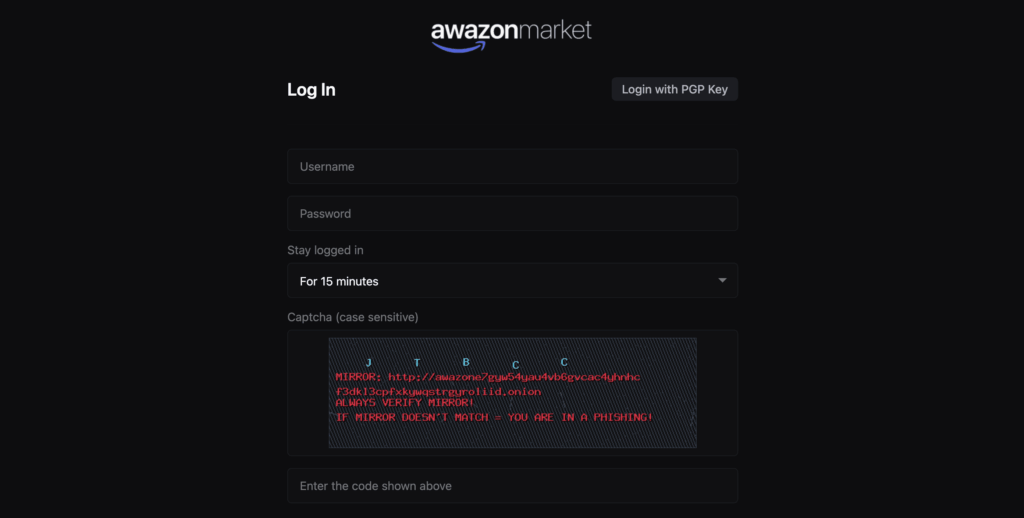
- Direct onion link 1: awazone7gyw54yau4vb6gvcac4yhnhcf3dkl3cpfxkywqstrgyroliid.onion/auth/register_now
- Direct onion link 2: awazonevlc63543fjvtli35bk2iopdyyaaytkmmiop5avny6b24uljqd.onion/auth/register_now
Awazon is one of the most well-known dark web marketplaces, often compared to an underground version of Amazon. Accessible via Tor and cryptocurrency, it facilitates the trade of illegal goods such as fake IDs, stolen credit card data, drugs, and hacking tools under the promise of anonymity.
Despite its criminal nature, Awazon features a polished, e-commerce-style design with vendor ratings, escrow services, dispute resolution, and even an AI assistant—earning it the label “the Amazon of the dark web.”
However, the sleek interface hides serious dangers. Authorities closely monitor such platforms, and users risk scams, data theft, legal action, or sudden loss of access if the market is shut down or compromised.
4. Tenebris
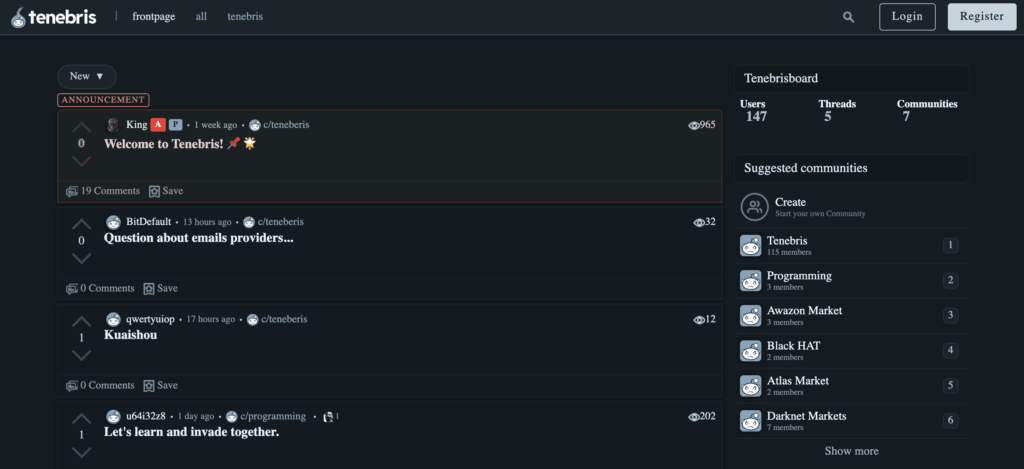
- Direct onion link: http://tenebrispoyfrcup4k24lciwrh4gc5735hmld4dweq7his7zh423opqd.onion/
Tenebris is a popular dark web forum where darknet users communicate to share news, mostly about markets, scam alerts, and law enforcement moves. It’s like a hub for darknet culture, market, and vendor reviews. One useful aspect of its community is that people here give warnings or alerts about upcoming scams or busts.
Just like the popular mainstream community Reddit’s subreddits, Tenebris is organized into communities where users talk about different topics. Like most of the other online communities, admins and moderators moderate it, but it’s not censored like others.
The platform looks good because of its reputation and ease of use, but remember that a lot of underground criminal activities online are planned on these forums. Tenebris backs communicating about privacy tools and cyber threats. However, again, platforms like these are mostly a hotspot for criminals to gather info, trade illegal stuff, and pull off fraud. Be cautious.
5. Ahmia
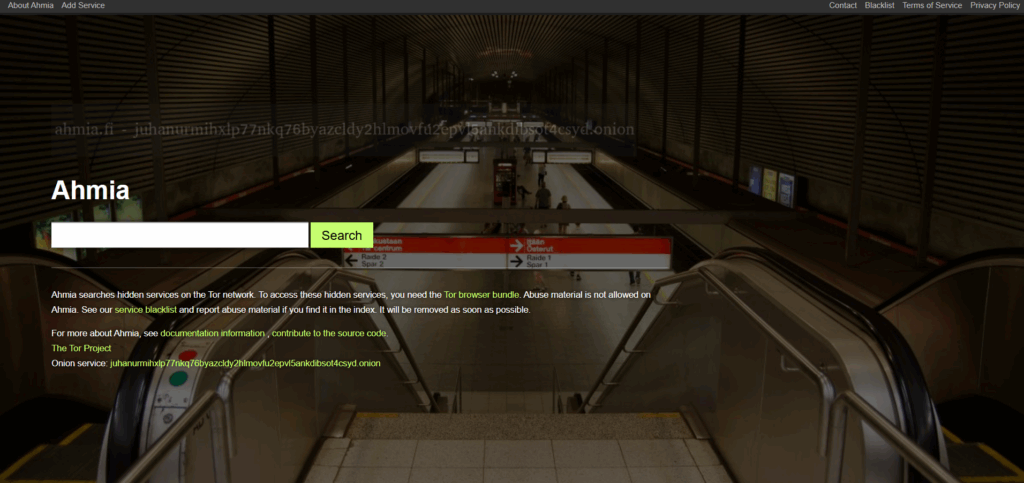
- Direct onion link: http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/
Ahmia is one of the most reputable and significant search engines on the Tor network. Originally created to curate hidden services on the Web, what makes this engine different from many others is that it does not allow illegal content (specifically child exploitative content) to be indexed, therefore giving users an extremely safe place to get started with their exploration of the dark web.
For first-time users, Ahmia is often the least intimidating starting point—it feels closer to a traditional search engine and is far less likely to surface disturbing content.
Supported by the community and engaged with numerous other Dark Web tools, Ahmia is at the forefront of attempting to maintain legitimate indexing, thus making it one of the most popular ways for researchers, journalists, and ethical hackers to find Onion sites and Dark Web sites.
Users are also able to submit their own .onion sites for indexing, allowing the community to have an avenue of ownership/empowerment of the legitimate uses of the Dark Web. Its mission to clean up the Dark Net and provide a platform for censorship-resistant services makes it a great, reliable resource.
6. Torch
- Direct Onion link: http://xmh57jrknzkhv6y3ls3ubitzfqnkrwxhopf5aygthi7d6rplyvk3noyd.onion/
Torch has been around longer than most other dark web search engines. This means it has built up one of the largest index collections of .onion sites.
On the plus side, Torch allows for searching through many .onion links that are no longer hosted, allowing you access to many older and unusual links, giving a unique perspective into how the dark web has changed over the years.
Unlike Ahmia, Torch does not function as an engine that actively filters dangerous material and illegal content. Thus, it is critical that users actively monitor themselves against exposure to any potentially compromising material returned by Torch.
Torch relies heavily on Functionality rather than Aesthetics when creating its interface, which gives it a vintage appearance associated with early 2000’s style search engines. As such, it is an excellent resource for performing thorough research, but it is highly advised that new users only search based on safe dark web links found on directories, as Torch is an unfiltered version of the hidden internet and requires that users take much greater precautions to maintain their security and privacy (including the disabling of JavaScript).
7. Haystack
- Direct link: https://haystacksearch.org/
Haystak is a highly regarded replacement search engine for use on the dark web. In addition to extensive Deep and Specialized Indexing capabilities, Haystak has created an Index of the dark web that may be among the best currently available.
Haystak’s ability to provide detailed retrievals for service on the dark web makes it particularly desirable to security researchers and threat intelligence analysts who perform ongoing searches for specific words or data leaks across large portions of the dark web/onion network. Haystak allows users to fine-tune their search parameters by providing customizable retrieval options for each user.
Since the Dark Web has a very dynamic nature, with continual addition/deletion of sites, it is beneficial for researchers to have at least additional resources, like Haystak, to track trends in this ever-changing environment.
As with any other search engine, links found through Haystak should be approached with caution and have their associated addresses cross-referenced against resources known to be trustworthy.
8. OnionWiki
- Direct link: https://onionwiki.com/
Although it isn’t an onion site itself, OnionWiki often serves as the first stop for users exploring the darker side of the internet. As the name implies, it functions as a directory of .onion websites, offering a basic roadmap for navigating the dark web. Inspired by the original Hidden Wiki, it compiles links to many well-known Tor-based sites. However, unlike Google, Yahoo, or even dedicated darknet search engines, OnionWiki doesn’t allow keyword searches—users can only browse a curated list of links.
While this straightforward directory claims not to collect user data and says it reviews the links it lists, additions and removals are made at the administrators’ discretion, often without notice. As a result, the directory can contain a mix of legitimate resources alongside risky or illegal websites, making it essential to verify the links carefully before clicking them.
9. ProPublica

- Direct onion link: https://www.propub3r6espa33w.onion
ProPublica is one of the nonprofit independent journalistic organizations based in America that specializes in investigative journalism designed to reveal corruption and abuse of power by government, business, and society. Its .onion site is the quintessential example of use of the Tor Network by an authentic organization and how to properly leverage the Dark Web for access to important stories and information.
Its primary purpose is to provide access to its articles for readers living in censored/repressive countries where readers cannot easily navigate to the ProPublica website using normal methods of access to the internet, as well as to protect the anonymity of those readers.
This represents one of the primary roles of the Tor Network: as a means of providing access to free press and human rights information. ProPublica is another must-have safe dark web link and an absolute necessity for any new user who wants to use the Tor Network in legitimate ways other than engaging in illegal activities.
10. BBC Tor mirror
- Direct onion link: http://bbcnewsv2vjtpsuy.onion/
The BBC Tor mirror’s news department, the UK’s national public broadcasting service, has created an official version of its news site available on the Tor Network. It was created to help circumvent government censorship in places where access to the BBC is limited or prohibited.
By providing access to free, independent global reporting through an .onion domain, the BBC supports the idea that anyone can receive the same quality of reporting, no matter where they happen to reside or what their country’s internet restrictions may be.
The BBC News onion site is very reliable as a trusted top dark web site that provides consistent coverage of significant world events and is open to anyone, regardless of where they live or the limitations placed upon them by their own country in terms of Internet usage.
11. The New York Times
- Direct onion link: https://www.nytimesn7cgmftshazwhfgzm37qxb44r64ytbb2dj3x62d2lljsciiyd.onion/
Following the lead of other major news organizations, The New York Times also hosts an official, verified .onion mirror of its primary website. Like the BBC and ProPublica, this service is a testament to the Dark Web’s ability to facilitate unrestricted information flow.
The NYT mirror ensures that its journalism remains accessible in countries where censorship is applied to independent media. For journalists, having a stable Tor address is also vital for receiving tips and maintaining communication with sources who require absolute anonymity.
It is another example of a high-authority, reliable service that belongs on any list of best dark web sites for those seeking legitimate access to world-class reporting.
12. Protonmail
- Direct onion link: http://protonmailrmez3lotccipshtkleegetolb73fuirgj7r4o4vfu7ozyd.onion/
Protonmail offers one of the highest levels of security and privacy for email services, utilizing End-to-End Encryption (E2EE), and operates under Swiss Privacy law. It has developed & maintains a dedicated Verified Onion service which allows users to access their encrypted email accounts over the TOR network, allowing for the highest possible level of security for their Protonmail email accounts.
When utilizing this service, both the origin of the communication and the actual content of the message are securely protected & encrypted through their combined use of TOR and ProtonMail’s end-to-end encryption. It is an essential tool for activists, journalists, and anyone handling sensitive communications, making it one of the top dark web sites for digital security.
13. SecureDrop
- Direct onion link: http://sdolvtfhatvsysc6l34d65ymdwxcujausv7k5jk4cy5ttzhjoi6fzvyd.onion/
The SecureDrop system is an open-source platform for anonymous submission of classified or whistleblower documentation to journalists. It has been implemented by many of the largest publications, including The Guardian, The Washington Post, and others.
The primary function of the service is to provide a truly anonymous method for sources to transfer sensitive data to the reporter assigned to their case. Each participating news organization has its proprietary installation of the SecureDrop system with its unique .onion address, which means that each installation is a private, secure installation accessible to the individual users of that publication.
The SecureDrop system uses Tor technology to provide complete anonymity for the source, while also ensuring that the data submitted to the publication is securely stored and has no association with the original source.
Consequently, SecureDrop provides the safest and most ethical means of communicating between sources and reporters, while simultaneously taking advantage of the anonymity features offered by the dark web.
14. Keybase
- Direct onion link: http://fncuwbiisyh6ak3i.onion/
Keybase is primarily known as an OpenNet service, but has made a strong entrance in the Privacy space as it pertains to Cryptographic Identity Verification due to its services to connect users with their various online Identifiers (like GitHub, Twitter, etc.) and their Public Key. Hence, it provides a verifiable Cryptographic Proof of who they are, even whilst being anonymous.
In the Dark Web, a service like this can be very helpful as it provides users with a way to verify the trustworthiness of other users. This creates a verified and encrypted communication pathway between users, which enables them to speak with greater confidence about who they are communicating with.
In addition to providing Secure Encrypted Communication Channels, Keybase also provides Encrypted File Sharing, Git Repositories, all protected using its robust security model, which provides developers/privacy advocates with strong resources.
15. Dread
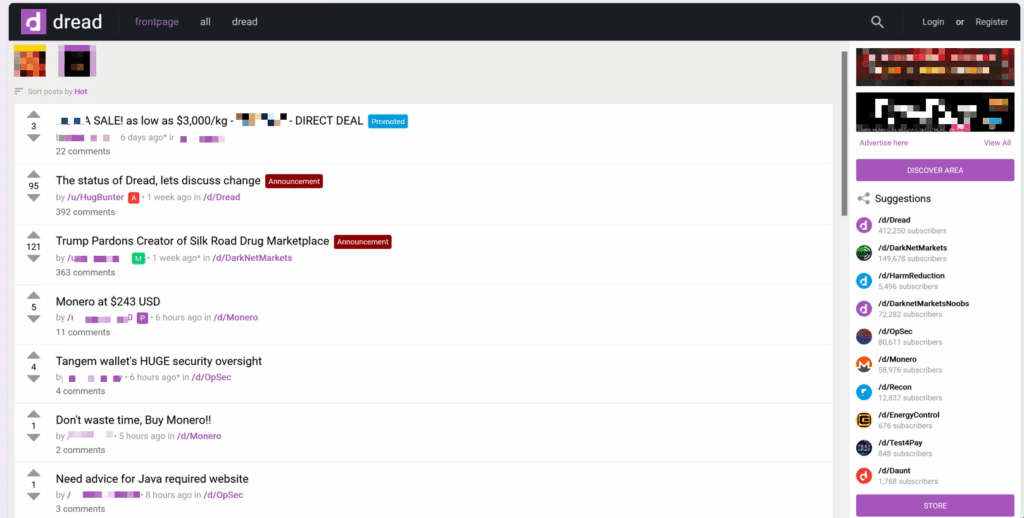
- Direct onion link: http://dreadytofatroptsdj6io7l3xptbet6onoyno2yv7jicoxknyazubrad.onion/
The Dread forum, the largest and most popular dark web community, is often compared to a dark web version of Reddit. It serves as a place where users can connect with like-minded individuals to discuss a wide variety of subjects related to drugs, technology, cybersecurity, etc.
Due to its highly accessible nature, Dread poses numerous threats to both users accessing this type of content and those looking for the information contained within it. Although Dread hosts valid discussions about technology and security, it also gives access to numerous types of illicit content, including illegal drug sale marketplaces.
Therefore, any individual wanting to study or analyze the dark web should utilize Dread, as it is the most reliable form of access to obtaining accurate intelligence about the overall landscape of the dark web. It is a prime example of the uncensored nature of the types of dark web websites that exist in this space.
16. SearX
- Direct onion link: http://ulrn6sryqaifefld.onion/
SearX is a privacy-focused metasearch engine accessible on both the clear web and the dark web. It is designed to protect user anonymity by blocking tracking cookies, ensuring searches are not influenced by personalization or profiling.
In addition, SearX transmits search queries using HTTPS POST requests, which helps prevent servers from recording or logging user data. This approach further strengthens privacy by minimizing the digital footprint left behind during searches.
17. OnionLinks
- Direct onion link: http://jaz45aabn5vkemy4jkg4mi4syheisqn2wn2n4fsuitpccdackjwxplad.onion/
Torlinks is a more curated and reliable alternative to the often chaotic Hidden Wiki. It functions as a traditional directory, categorizing links by topics like news, financial services, email, and social networks.
Its primary value lies in its attempt to keep its listed links up-to-date and verified, addressing the huge problem of dead or phishing .onion sites on the network. For new users, starting with a vetted list like the one found on Torlinks provides a much safer introduction to exploring legitimate onion sites and dark web websites without the immediate exposure to extremely risky content.
Even with user-chosen curated lists, diligence is the last line of protection for users. Always check to see that your security settings.
18. Riseup
- Direct onion link: http://vww6ybal4bd7szmgncyruucpgfkqahzddi37ktceo3ah7ngmcopnpyyd.onion/en
Riseup is a collaborative organization created by people doing activism to provide secure, encrypted means of communication via the internet and assist in bringing change within society.
It provides secure email and chat services via the internet as well as Virtual Private Network (VPN) services, and is often used by activists, journalists, and human rights organizations fighting repressive regimes.
Additionally, Riseup uses the Dark Web to keep these important tools available when governments block access to their sites on the clear web. Riseup is one of the most trusted services within the privacy community and serves as a great example of how ethical use of the dark web can provide a safe and protected means of communication.
19. The CIA
- Direct onion link: http://ciadotgov4sjwlzihbbgxnqg3xiyrg7so2r2o3lt5wz5ypk4sxyjstad.onion/
The United States Central Intelligence Agency (CIA) has developed its .onion site on Tor. This might seem very strange, given that the site’s goal is to allow people around the globe to communicate with them in a secure and anonymous way to submit intelligence, tips, or information.
The CIA has set up its own website using the Tor Network so that individuals’ information is protected and allows individuals to send documents through the Tor Network without revealing their identity. By giving individuals access to the Tor Network, the CIA has been able to demonstrate its confidence in the functionality of the Tor Network’s anonymity as long as it is properly set up.
Plus, in giving individuals access, they have validated the use of Tor as a secure means to communicate anonymously in high-risk situations.
20. Facebook Onion site
- Direct onion link: https://www.facebookcorewwwi.onion/
Facebook, run by Meta, operates an official Tor mirror of its main site. This was created primarily for users in countries where the social network is blocked due to government censorship, or for those who simply wish to bypass regional restrictions while accessing the social network.
While Meta’s own data collection practices are well-documented, accessing their site via Tor ensures that the connection details (your IP address) are hidden from both the ISP and the network itself. This is another example of a top dark web site that allows users to perform common internet tasks with an added layer of connection anonymity.
21. Archive.today
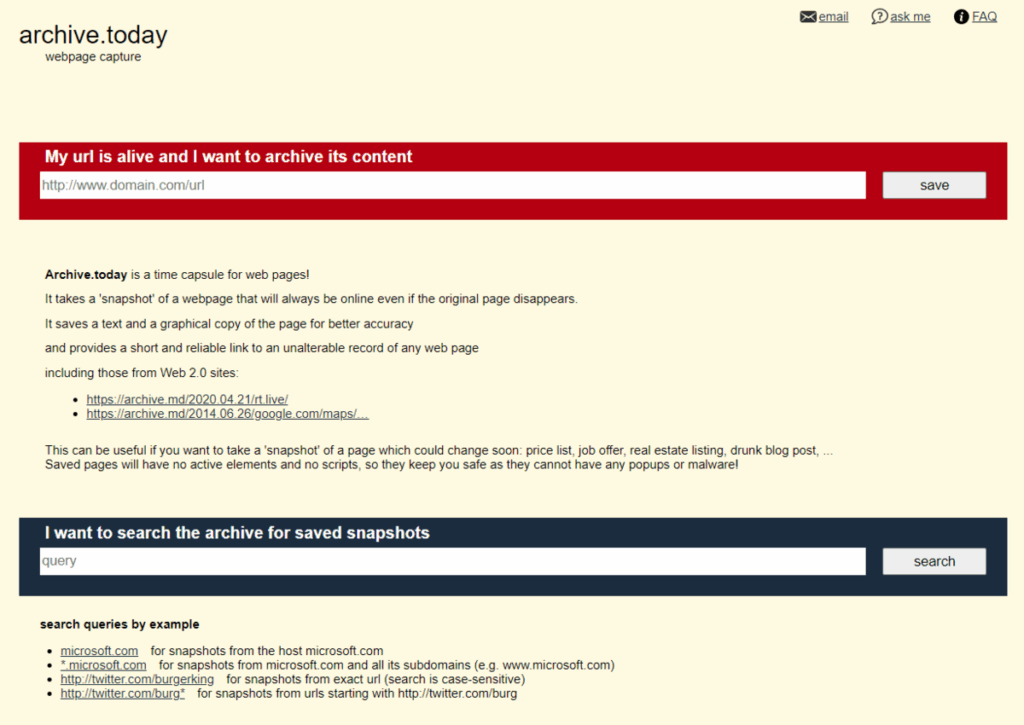
- Direct onion link: http://archivecaslytosk.onion/
Archive.today offers users an opportunity to literally “go back in time”, to see what a website looked like as it was originally published. The tool is very helpful for researchers, journalists, and security professionals working within the realm of the dark web.
Because .onion domains can be removed, seized, or go offline unexpectedly, Archive.today provides a reliable way to save data and content from those sites. Using Archive.today helps you preserve evidence, content, or information that might otherwise be lost due to the dark web’s unpredictable nature.
22. Sci-Hub
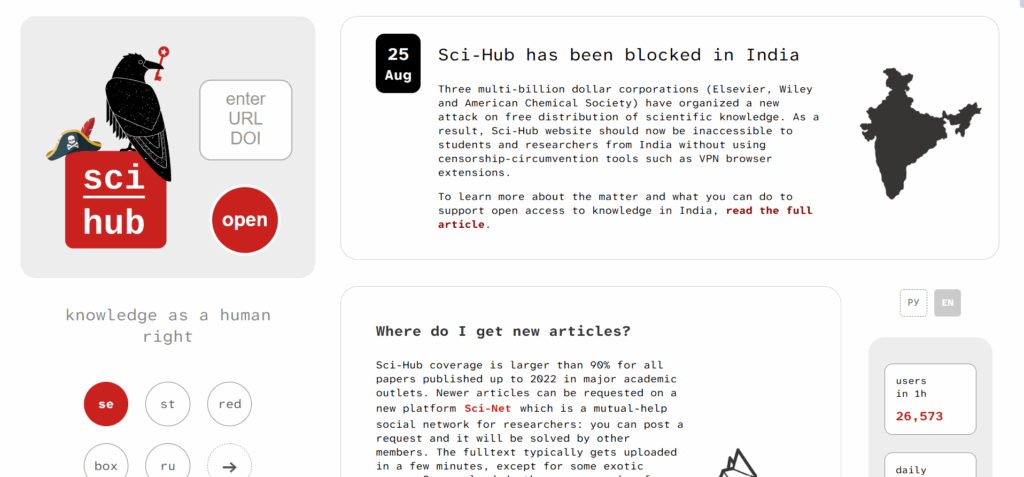
- Direct onion link: http://scihub22266oqcxt.onion/
Sci-Hub serves as the dark web’s version of a massive online library, giving millions of users free access to legally protected academic papers, books, and scientific resources.
It has attracted controversy over the years due to its practice of challenging the current model of academic publishing, but it is a very important resource for researchers from developing countries as well as those who do not have access to universities.
The benefit of operating anonymously on the dark web has allowed them to withstand legal action taken against them by the major publishing companies. It represents the “information freedom” aspect of the dark web.
23. ExoneraTor
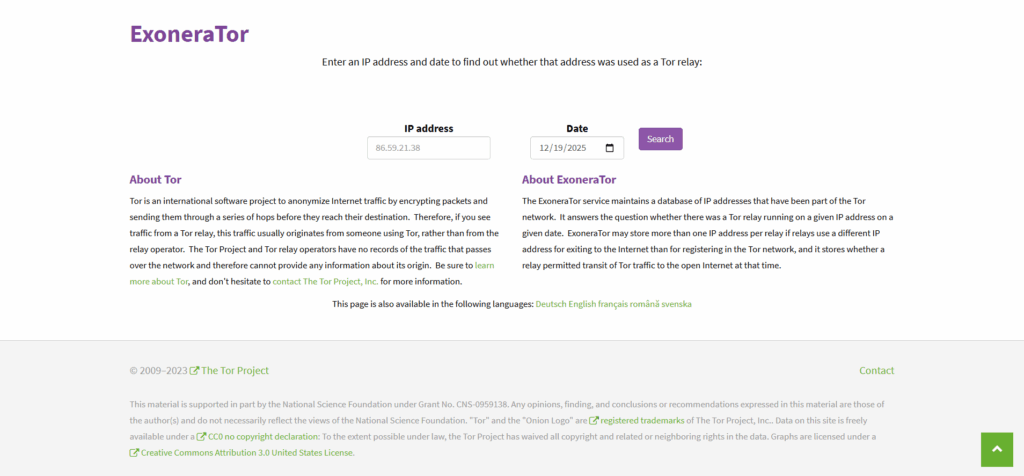
- Direct onion link: http://hctxrvjzfpvmzh2jllqhgvvkoepxb4kfzdjm6h7egcwlumggtktiftid.onion/exonerator.html
The Tor Project created ExoneraTor to let users check whether a specific IP address served as a Tor relay on a given date. Server operators, law enforcement, and academic researchers most commonly use ExoneraTor to identify potential malicious activity on the Tor network.
If an IP address is confirmed as a Tor exit node during the period of an incident, the confirmation supports the defense of the user. Thus, it offers a critical means of transparency into the commitment by the Tor Project to being accountable.
24. Tor Metrics
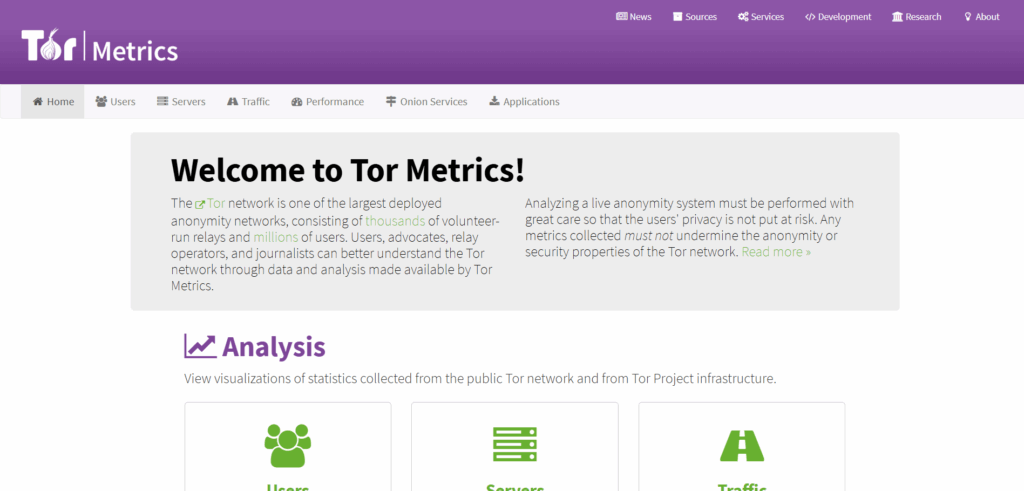
- Direct onion link: http://hctxrvjzfpvmzh2jllqhgvvkoepxb4kfzdjm6h7egcwlumggtktiftid.onion/
Tor Metrics is the Tor Project’s official source for statistics and information regarding the use of the Tor network. It provides public access to the number of users and trends in usage broken down by geographic location, as well as the number of individual relays that are operational.
The Tor Project uses Tor Metrics to measure the performance and security of its network, and researchers from around the globe rely on it to measure the international impact of the Tor network.
Visiting Tor Metrics provides a fascinating, technical look “Under the hood” of the dark web, showing its real-world usage and resilience.
25. Tails
- Direct link: https://tails.net/
Tails is a privacy-focused Operating System built by the Tor Project itself. Users can boot Tails off of USB storage devices, while it forces all of their outbound connections through Tor. Unlike a standard operating system, Tails leaves no trace or evidence on the computer after you use it. Tails also has several pre-configured top-of-the-line privacy tools.
The official Tails website provides both a regular site and an .onion address, allowing users to download the Tails operating system and access documentation without being tracked. For those wanting maximum safety when searching through the best dark web sites, Tails will be the best possible environment.
26. Deep Web Radio
- Direct onion link: http://76qugh5bey5gum7l.onion/AnonyJazz
Deep Web Radio is a dark web–based streaming platform that plays a wide range of music genres around the clock. It allows users to listen anonymously, making it a unique entertainment option within the privacy-focused dark web environment.
Beyond streaming, Deep Web Radio also lets listeners submit and share their own playlists. This interactive feature fosters a rare sense of community in a space that typically emphasizes isolation over social engagement.
Surface web vs dark web vs deep web: Getting to know various layers of the internet
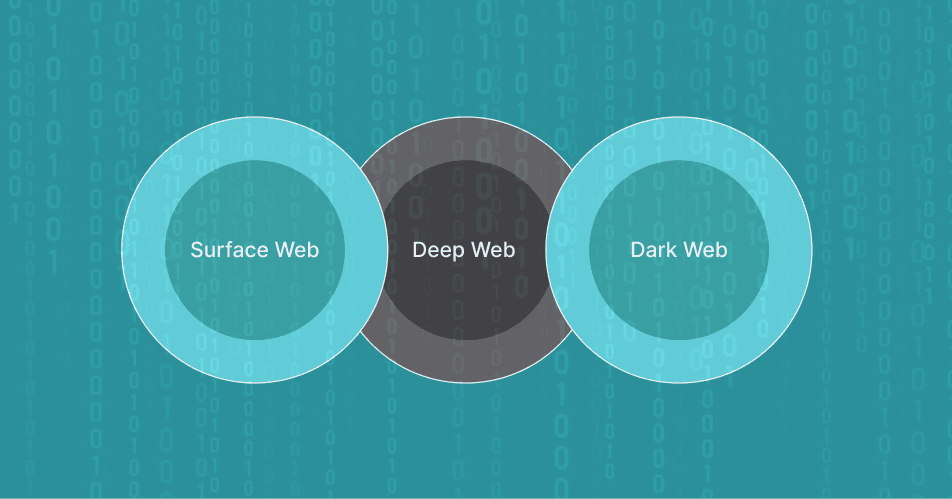
This is where it often gets tricky because many still find both terms (deep web and dark web) to be confusing. To put it simply:
- Surface web: This is what you use daily. It’s the stuff that shows up on Google and other search engines. It’s news sites, social media, and anything you don’t need a password to get to. The surface web covers about 5% or less of the total internet.
- Deep web: The deep web comprises approximately 90 – 95% of the total internet. The majority of online data resides here, and users generate a significant portion of it. This includes your private email inboxes, banking portals, private corporate databases, and paywalled subscription content. It generally does not harm users; it only remains private or requires a password for access. You access it every day without special tools.
- The dark web: It’s a whole different thing – picture it as a tiny, hidden corner inside the Deep Web. You won’t find it by accident because it stays hidden by design—only special tools like the Tor Browser or I2P, along with unique .onion addresses, allow access. These tools assure both you and the website stay anonymous.
Knowing this difference helps when talking about this stuff. Most of the internet is deep, but the dark part is tiny and needs the special security stuff we’re talking about.
Types of dark websites
The dark web has all sorts of sites, just like the regular internet, but a lot of them focus on keeping you private and secure.
| Type | Description | Key Examples |
| Search Engines | You can’t find .onion sites with Google, but there are search engines out there that dig them up. Ahmia, for example, cuts out illegal stuff. Torch, on the other hand, pretty much leaves everything in. | OnionFind, Ahmia, Torch, Haystak |
| Directories/Wikis | Human-curated lists of active dark web links that help users navigate the volatile network landscape. | OnionWiki, OnionLinks, Deep Web Links |
| Secure communication | So, there are platforms that apply encryption for private chats, emails, and sending files; a lot of times, you will find it hosted on Tor to make things extra safe. | SecureDrop, Protonmail, Riseup, Keybase |
| News and Media Mirrors | So, there are platforms that apply encryption for private chats, emails, and sending files; a lot of times you will find it hosted on Tor to make things extra safe. | ProPublica, The New York Times, BBC News |
| Forum and social networks | Online discussion groups focused on topics such as privacy, security, the illegal drug trade, and other aspects of life without censorship. | Tenebris, Dread, The Hub Forum |
| Marketplaces (informational) | .onion mirrors from big news places let reporters post stuff, and readers get to it without getting censored. | So, there are platforms that apply encryption for private chats, emails, and sending files; a lot of times, you will find it hosted on Tor to make things extra safe. |
How to find new, active dark web links

Here’s how you can find dark web links that actually work:
Dark Web links usually don’t last; they’re either shut down or move around to stay hidden. So, finding new, working links means you can’t just rely on old lists. You have to be active about it.
1. Dedicated search engine crawling
The most effective method is using specialized dark web search engines that actively crawl the network:
- OnionFind: Best for reliable, filtered, and safer search results.
- Torch, Ahmia, Haystak: Best for comprehensive, deep, and often unfiltered results.
These search tools use different crawlers than Google, actively looking for the .onion address structure.
2. Monitoring trusted link aggregators (directories)
Rely on frequently updated link lists like OnionWiki, OnionLinks, and other vetted directories. These communities often verify the operational status of links, saving you the time and risk of hitting phishing sites or malware traps.
3. Using onion-location headers
The Tor Browser supports a feature called Onion-Location. If a regular website (like a .com or .org) also runs an official .onion mirror, it can let people know with a header. When you go to the regular site, Tor Browser will show a purple pill in the address bar that says .onion available.
Click it, and you can quickly and safely go to the real hidden service. This is one of the safest ways to find a site’s new link.
4. Forums and social monitoring
Security researchers and dark web analysts usually keep an eye on forums like Dread and other smaller online groups. Users often post and discuss new links here first, especially for marketplaces or services, giving early access to information, though this approach carries the highest risk.
How to access dark web links: A Straightforward guide

So, you’ve got the right tools. Follow these steps to get started with dark web links. (Note: The following guide is for desktop. If you want to use your smartphone, the process involves different apps and settings. We cover it in detail in our guide easy steps to access dark web on your phone safely.)
- Fire up your VPN (one from a reliable provider, like NordVPN), choose a server from a privacy-friendly country (think Switzerland or Iceland), and connect. Once the VPN is active, it’ll scramble all your traffic even before it reaches Tor. That’s your Tor-over-VPN safety net right there.
- Shut down anything you don’t need. Seriously, close out all those extra apps, especially the ones poking around your location or personal files, or anything that’s not using encryption. The fewer things running, the fewer ways someone can sneak into your system.
- Open the Tor Browser. Do not maximize the window; keep the default window size to avoid giving away monitor resolution (a potential fingerprinting method).
- Go to the security settings and set the slider to “Safest.” This disables JavaScript and other dangerous elements that can be exploited by malicious Onion sites and dark web websites.
- Once you’re connected to Tor Browser, head over to a site like ipleak.net. Look for your IP address—if it’s one from a Tor Exit Node and not your actual one, you’re good to go. That means Tor’s doing its job.
- Grab a .onion address from a reliable directory or one of the search engines we mentioned, like OnionFind.com. Copy it—don’t just click random links.
- Type the address right into Tor. Keep away from downloading anything or giving out your personal info. Leave immediately if something feels off.
Alternative methods to access dark web links

In addition to making Tor the best method for accessing .onion domains, different networks make up the dark web. There are many anonymous/encrypted overlay networks hosting dark web links (darknets).
1. I2P: Invisible Internet Project
I2P is an anonymous Peer-to-Peer (P2P) networking system. It achieves anonymity through Garlic Routing, a more complex method than Tor’s Onion Routing, and hosts its own naming conventions called Eepsites (an eepsite is I2P’s equivalent of a Clearnet or .com website).
- Unlike Tor, I2P has specific design goals when accessing anonymous services (eepsites) versus exiting to the public internet (Clearnet). Speed is extremely important within I2P; therefore, the focus is heavily on internal communication, file sharing, and torrenting between users on the I2P network.
- To use I2P, you must have an I2P router installed. Unlike Tor, I2P does not allow access to .onion links. Instead, I2P allows for access to .i2p domains.
2. Freenet (or Hyphanet)
Freenet provides an environment for publishing protected, anonymous content and operates as a peer-to-peer, censorship-resistant platform.
- The biggest difference between Freenet and other P2P systems is that Freenet is a file storage and retrieval system. The ability to be anonymous comes through encryption, fragmentation and distribution of files across multiple nodes within the Freenet network. This makes it so difficult for a single entity to either censor files or know their location.
- Freenet operates independently of both Tor and I2P. It also features its own unique user content area, and users cannot access it through a web browser or standard application.
3. Tails OS (The Safe OS)
Tails OS isn’t really a network; however, it is a Linux OS and runs “live” from an external USB device.
- The biggest difference is how Tails will automatically route all your applications and all of your network traffic over the Tor Network, while at the same time leaving behind no trace on the computer after a shutdown. Therefore, Tails provides you with the most secure way to access top dark web sites.
Legal and ethical aspects

Currently, according to some laws, legal use of Tor exists. However, as with any other application, there are the same legal and ethical issues associated with it.
Anyone wishing to use a Tor browser should be aware that there may be legal ramifications as well as ethical considerations surrounding their utilization of darknet websites.
Jurisdictional laws
Depending on where you’re located, the legality related to specific types of content may vary greatly. Streaming service violations (download, etc.) or violations related to certain types of political speeches could be subject to very different interpretations based on where you live. This matters if you’re in a censored country.
Be absolutely sure to comply with the applicable laws within your locality and, if you’re using a privacy tool to access the dark web, understand that it doesn’t protect you from prosecution under local law in relation to any downloaded/media or political content you may view.
Reporting of illegal content
If you come across something that is blatantly illegal, such as CSAM (child sexual abuse material) or extreme violence, then you have both an ethical obligation and a legal obligation to report it, whether through contacting NCMEC (National Center for Missing and Exploited Children) or through your local law enforcement.
Do not download the material; simply record the URL you found it on, plus any other metadata you might obtain securely.
Ethical research
As a journalist, cybersecurity professional, or anyone tasked with researching data via the dark web, this is often a necessary and sometimes the only means to gather threat intelligence, content access, etc.
However, conducting transactions, attempting to hack, or using any method to distribute malware clearly and without exception crosses the boundaries of ethical and legal activity.
How to use Tor with a VPN (Tor-over-VPN)

For maximum safety and anonymity—a critical step that follows our PS SOP—you must use a VPN in tandem with Tor. Using a rigorously tested VPN is crucial; we’ve reviewed the top options in our best dark web VPN guide. This method, known as Tor-over-VPN (or Onion-over-VPN), prevents your ISP or network monitors from knowing that you are connecting to the Tor network.
This setup offers convenience and a high level of privacy, making it a simple and efficient way to use the Tor network.
Step-by-step guide to Tor-over-VPN connection
| Step | Action | Why it matters |
| Start with your VPN | Use your premium, no-log VPN and connect to the server of your choice (ideally a server that resides within an area that provides a level of privacy). | Doing this hides that you’re on Tor. Your internet company (and maybe the government) will just see a secure VPN, not the thing that says you’re using Tor. |
| Launch your Tor browser | After establishing a successful VPN connection, you can now launch the Tor Browser. | Your connection process will begin (the three hops that will transport your web activity through the Tor network). Since the IP address you are using to connect to the Tor network is that of the VPN server, there is now no way of knowing the sender’s IP address. |
| Verify the circuit | Once the browser is connected, click the green onion icon in the URL bar to view the Tor Circuit. | You will see three random relay nodes (Guard, Middle, Exit). The first node in the circuit (the Guard) will only see your VPN’s IP address, never your real one. |
| Check your security | Go to a simple IP checking site (i.e., ipleak.net) within your Tor browser. | The IP shown should be the IP of the Tor Exit Node, not your original ISP or VPN IP, and not the same as your real IP address. This indicates that your Tor over VPN connection was successful. |
Legalities on the use of the Tor network

The legalities surrounding Tor are at the heart of arguments regarding the legitimacy of the dark web. Almost everywhere in the world, you will find an answer of “no” when it comes to whether Tor is illegal.
Tor is not an illegal activity
- Using the Tor Browser is completely legal: Only a few countries have made it illegal to download, install, or use the Tor Browser. Developers built the Tor Browser as open-source software to provide privacy, enable secure communications and services, and allow users to remain anonymous.
- The original purpose of Tor: The main intent of Tor’s founding was as a means for both secure and highly private communications between the many branches of the US military and intelligence. Journalists, humanitarian workers, activists, and law enforcement professionals legitimately use it to communicate privately and securely without allowing outside parties to observe or monitor their communications.
- The exception: The only time the legality of using Tor comes into question is when it involves illegal activity that the user is engaging in while using the services provided by Tor (like purchasing illegal drugs, distributing material involving child exploitation, hacking). The use of Tor in an effort to perpetrate these activities is a criminal offense, and, therefore, using Tor will not give the user immunity from prosecution for their illegal activity.
- Government monitoring: Keep this in mind, although Tor is a legitimate service available to use, many different countries (like China, Russia, and Iran) see the usage of encrypted services (or other means) to conceal their identity as possible “red flags” to monitor you by their government agency. Therefore, consider utilizing a combination of Tor and a VPN to protect your connection from any potential government monitoring, particularly when you are located in a censored country.
FAQs
Share this article
About the Author
Rebecca James is an IT consultant with forward thinking approach toward developing IT infrastructures of SMEs. She writes to engage with individuals and raise awareness of digital security, privacy, and better IT infrastructure.
More from Rebecca JamesRelated Posts

What is Dark Web? How It Works, Its Legality, and Dual Nature
It’s okay to imagine the internet like a giant, magical ocean. There are parts of this ocean you can...
14 Best Dark Web Monitoring Tools and Solutions in 2026
KEY TAKEAWAYS By monitoring the dark web, organizations can stay protected and remain on the latest ...

11 Best Dark Web News Sites in 2026
KEY TAKEAWAYS If you live in a country where you don’t have internet freedom and face extreme ...
The 17 Best Dark Web Marketplaces in 2026
KEY TAKEAWAYS Accessing any darknet marketplace is dangerous because it is known to be a hub for ill...

Dark Web vs. Deep Web: What’s the Difference?
KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. The major difference be...
4 Easy Steps to Access Dark Web on Your Phone Safely in 2026
The dark web has been a source of mystery and caution, and accessing it seems complex. Let...